AWS NAT Gateway Cost Too High — How to Reduce Your Data Transfer Bill
AWS billing has gotten complicated with all the noise flying around about cloud cost optimization. Everyone’s got a hot take. But as someone who has spent five years crawling through engineering teams’ AWS bills, I learned everything there is to know about NAT Gateway costs the hard way. Today, I will share it all with you.
Here’s the short version: roughly 80% of the bloated AWS bills I’ve seen have one thing in common. The NAT Gateway line item. You set it up, you forget about it, and then one Tuesday morning the invoice arrives. $2,000. $5,000. I’ve watched a perfectly reasonable startup-sized workload ring up $15,000 in a single month. That’s when people start calling me.
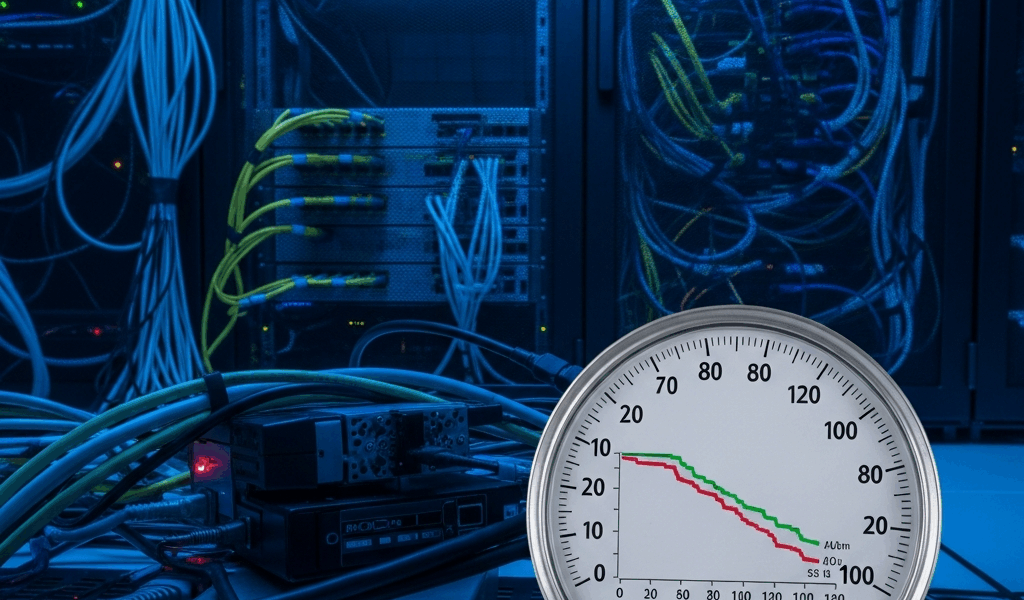
The charges are brutal and they come from two directions. AWS bills $0.045 per gigabyte processed through a NAT Gateway — and separately charges $0.045 per hour per availability zone just for having the thing running. Three NAT Gateways for a standard three-AZ production setup? That’s around $1,000 a month before a single byte moves. Then your application starts pushing S3 requests, DynamoDB calls, CloudWatch Logs, ECR image pulls — all of it — straight through the NAT Gateway by default. The meter doesn’t stop.
What follows is every fix I’ve actually deployed in real production environments. Some cost nothing. None require touching application code. Together, they’ve knocked NAT Gateway costs down 30–70% for the teams I’ve worked alongside.
Why Your NAT Gateway Bill Is So High
But what is a NAT Gateway, really? In essence, it’s a managed service that translates private IP addresses to public ones so instances in private subnets can reach the internet. But it’s much more than that — it’s also a billing surface that touches nearly every AWS service call your application makes.
That’s what makes the NAT Gateway pricing model so punishing to teams who haven’t mapped their traffic flows. The hourly charge hits regardless of usage. Run three gateways — one per AZ, which is standard practice for redundancy — and you’re spending roughly $0.135 per hour. That’s around $97 per month just in baseline charges. Totally before data processing enters the picture.
Then the real problem shows up. Your application is almost certainly routing traffic through the NAT Gateway that has absolutely no business being there. S3 requests. DynamoDB reads. CloudWatch metrics. ECR image pulls on every container deployment. Every single one of those flows accumulates data transfer charges at $0.045 per gigabyte.
I learned this firsthand — don’t make my mistake. Early on, I deployed a microservices stack without properly auditing traffic flow. One service alone was pushing 2TB per month through the NAT Gateway just to reach S3. That’s roughly $90 a month for traffic that could have been completely free. Multiply that across a dozen services running nightly batch jobs, and you’re suddenly staring at hundreds of dollars in charges that shouldn’t exist.
The first move is always visibility. Enable VPC Flow Logs and route them to CloudWatch Logs or an S3 bucket for analysis. Filter for traffic leaving private subnets destined for 0.0.0.0/0. The patterns become obvious fast — large file transfers, repetitive API calls hammering the same endpoints, spikes tied to scheduled jobs. The answers are in the logs. They always are.
Fix 1: VPC Gateway Endpoints for S3 and DynamoDB
This is the biggest cost killer. Genuinely.
A Gateway Endpoint creates a private connection from your VPC directly to an AWS service — bypassing the NAT Gateway entirely. For S3 and DynamoDB, these endpoints are free. No hourly charges. No data transfer fees. Your instances communicate with these services as if they were local, and the traffic never touches the public internet or your NAT Gateway budget.
Setup takes around 10 minutes. Open the VPC console, navigate to Endpoints, select the S3 gateway endpoint type, choose your VPC and route tables, and attach it. Done. No application code changes. Your existing SDK calls to S3 and DynamoDB keep working identically — except now they’re not burning through your NAT Gateway at $0.045 per gigabyte.
For most accounts, this single fix cuts NAT Gateway costs by 30–50%. I’ve seen data transfer volumes drop by 500GB per month after a single Gateway Endpoint deployment. That’s $22.50 per TB saved, multiplied across however many services you’re running.
One thing worth noting: if you run Lambda functions pulling dependencies from S3, or batch jobs reading millions of DynamoDB records, the savings get even more dramatic. A fintech team I worked with had a nightly reconciliation job moving 3TB through the NAT Gateway to hit DynamoDB. After the Gateway Endpoint went in, that traffic disappeared from the bill entirely. Gone.
Check your route tables carefully, though. The endpoint has to be associated with every route table that has resources needing access. I’ve seen teams create the endpoint, scratch their heads wondering why traffic is still routing through the NAT — usually a forgotten route table attachment. VPC Flow Logs will confirm whether it’s working.
Fix 2: Interface Endpoints for Other AWS Services
Gateway Endpoints only cover S3 and DynamoDB. For everything else — ECR, CloudWatch Logs, CloudWatch Metrics, STS, Secrets Manager, Systems Manager Parameter Store — you need Interface Endpoints. Different animal entirely.
Interface Endpoints spin up elastic network interfaces inside your VPC that act as private proxies to the service. They’re not free. Each one runs $7.20 per month, plus $0.01 per gigabyte processed. That’s still five times cheaper than routing the same gigabyte through a NAT Gateway.
The math is pretty clean. If you’re transferring more than 720GB per month to a given service through the NAT Gateway, the Interface Endpoint pays for itself. For high-traffic environments, that threshold gets crossed in the first week of the month.
ECR is usually the first candidate I look at. Container image pulls are heavy — easily 50–200GB per month depending on image sizes and how often deployments happen. An ECR Interface Endpoint costs $7.20 monthly. At $0.01 per gigabyte through the endpoint versus $0.045 through the NAT, the savings start immediately.
CloudWatch Logs is the other high-volume offender. Even modest applications push gigabytes of logs through the NAT Gateway every month. A CloudWatch Logs endpoint redirects that traffic cheaply and efficiently.
I’m apparently someone who starts with ECR and CloudWatch Logs, and that approach works for me while jumping straight to Parameter Store never does. Parameter Store and Secrets Manager are lighter weight — worthwhile if you’re calling them hundreds of times per minute, less urgent otherwise. STS is genuinely high volume if your workloads assume IAM roles regularly, since every temporary credential request flows through it.
Setup is more involved than Gateway Endpoints. You’ll create the endpoint, configure security groups to allow HTTPS from your VPC CIDR, confirm private DNS is enabled — that’s a checkbox in the endpoint configuration — and modern AWS SDKs handle DNS resolution automatically from there. No application config changes required in most cases.
Fix 3: Reduce Cross-AZ NAT Traffic
This fix is subtle. It also quietly destroys bills when ignored.
Picture this: Service A runs in AZ1. Service B runs in AZ2. Both are in private subnets. When A calls B, the traffic crosses the AZ boundary — and AWS charges $0.02 per gigabyte for that cross-AZ transfer, on top of the NAT Gateway processing charges. You’re paying twice for the same data movement.
The standard answer is one NAT Gateway per AZ, keeping inter-service traffic within zone boundaries. That adds hourly charges — three gateways instead of one — but at scale, the cross-AZ savings outweigh the baseline cost increase. You have to run your specific numbers, though.
Example: moving 1TB per month across AZs through NAT Gateways costs $20 in cross-AZ transfer fees alone. Add processing charges through two gateways and you’re closer to $90. Shift to a per-AZ architecture where services prefer same-zone endpoints, and that figure drops substantially.
The tradeoff is real engineering effort. Services need awareness of AZ locality. That might mean AWS Cloud Map for service discovery, application-level routing preferences, or local caching layers. Not always worth the work for medium-traffic applications. Calculate the potential savings first, then decide whether the complexity earns its keep.
Fix 4: Move Workloads to Public Subnets Where Appropriate
Probably should have opened with this section, honestly. It’s less scary than teams assume.
Some workloads genuinely don’t need private subnets. Lambda functions. ECS tasks that don’t benefit from IP obscurity. Batch jobs that have no inbound exposure requirements. If a Lambda function sits behind a security group that denies all inbound traffic, it’s not meaningfully more exposed in a public subnet than a private one — but it no longer touches the NAT Gateway at all. Zero processing charges. Zero involvement.
This isn’t about abandoning security. It’s about honest architecture. Matching the network design to actual security requirements rather than reflexively defaulting every resource to a private subnet because that’s how the last template was configured.
I worked with an organization running daily ETL pipelines in Lambda. All of it deployed in private subnets — historical decision, nobody questioned it. Moving those functions to public subnets with locked-down security groups and minimal IAM roles cut their NAT Gateway data transfer by 40% overnight. Same security posture. Zero new risk. Just a smaller bill.
Start by auditing which private subnet workloads actually require the private subnet. Most organizations find 10–30% of those resources could move public without any meaningful security change. That’s free savings sitting in the architecture diagram.
Combining These Fixes
So, without further ado, let’s dive into how these stack together — because individually each fix helps, but the real movement comes from layering them.
The pattern I’ve seen work consistently: Gateway Endpoints first, since they’re free and high-impact. Then Interface Endpoints for the highest-volume services — ECR and CloudWatch Logs usually. Cross-AZ architecture changes next, if the math justifies it. Public subnet migrations last, after the audit is done.
That’s what makes this approach endearing to us infrastructure folks — it’s incremental. You don’t have to redesign the entire network to see results. One team I worked with dropped their monthly NAT bill from $8,000 to $1,200 over six weeks. Another went from $3,500 to $600. Both did it in phases, starting with the free fixes.
Your traffic patterns are different, so your results will be too. VPC Flow Logs analysis is non-negotiable as the starting point — you can’t optimize what you haven’t measured. Enable them, let them run for a few days, and the biggest cost contributors will surface quickly. From there, the fixes apply themselves.
The investment is small. The payoff is consistent. The bill next month will prove it.


Stay in the loop
Get the latest team aws updates delivered to your inbox.